US Electric Grid Hacked: Perpetrators Could Have Shut Down The System
by
Tyler Durden
Sun, 01/13/2019 - 13:50
Authored by Mike Shedlock via MishTalk,
Hackers broke into the US electric grid with spearphishing techniques targeting contractors with system access.
The Wall Street Journal has a detailed report out regarding a sophisticated, and successful attack by hackers into the US electric grid. The hackers could have temporarily shut off power.
Hackers broke into the US electric grid with spearphishing techniques targeting contractors with system access.
The Wall Street Journal has a detailed report out regarding a sophisticated, and successful attack by hackers into the US electric grid. The hackers could have temporarily shut off power.
The
Journal claims Russia is responsible. I hate such assumptions. In the
absence of hard proof, the hack could have come from China, North Korea,
Israel, or even the US. Even if Russian hackers did this, there is a
difference between "Russian" and "Russia".
Please consider America’s Electric Grid Has a Vulnerable Back Door—and Russia Walked Through It.
The excuse: "The tools and tactics suggested the perpetrators were Russian."
It's a bit of a leap to go from that assumption to the WSJ headline.
Please consider America’s Electric Grid Has a Vulnerable Back Door—and Russia Walked Through It.
Early victims
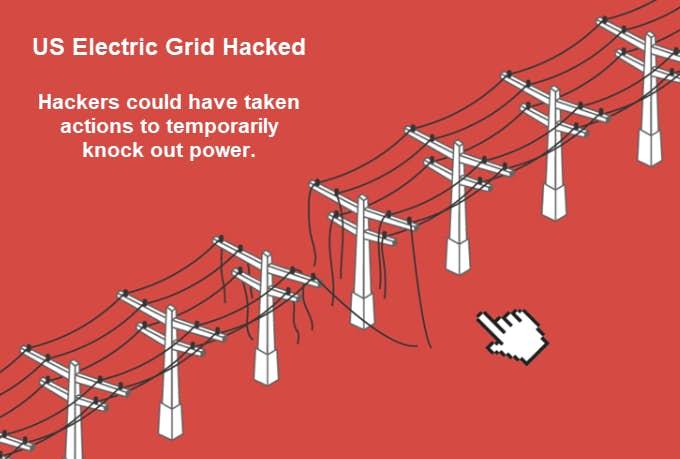
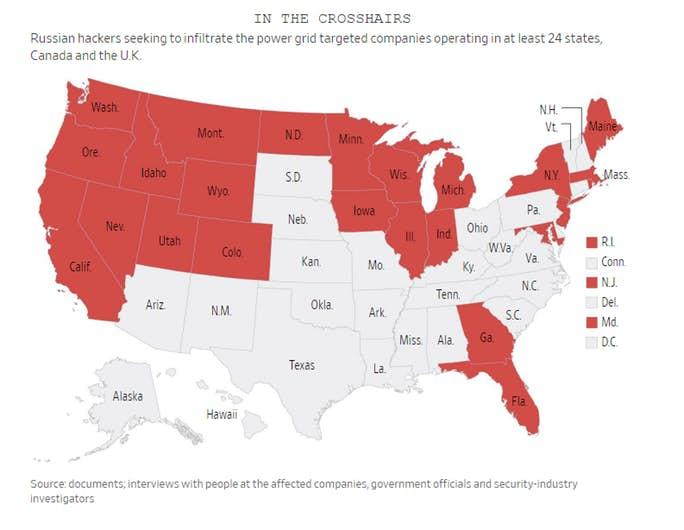
In the summer of 2016, U.S. intelligence officials saw signs of a campaign to hack American utilities, says Jeanette Manfra, assistant secretary of Homeland Security’s cybersecurity and communications program. The tools and tactics suggested the perpetrators were Russian. Intelligence agencies notified Homeland Security, Ms. Manfra says.
Mr. Vitello of All-Ways Excavating has no idea how the hackers got into his email account. He doesn’t recall reading CFE’s websites or clicking on tainted email attachments. Nonetheless, the intrusion was part of the Russian campaign, according to the security companies that studied the hack.
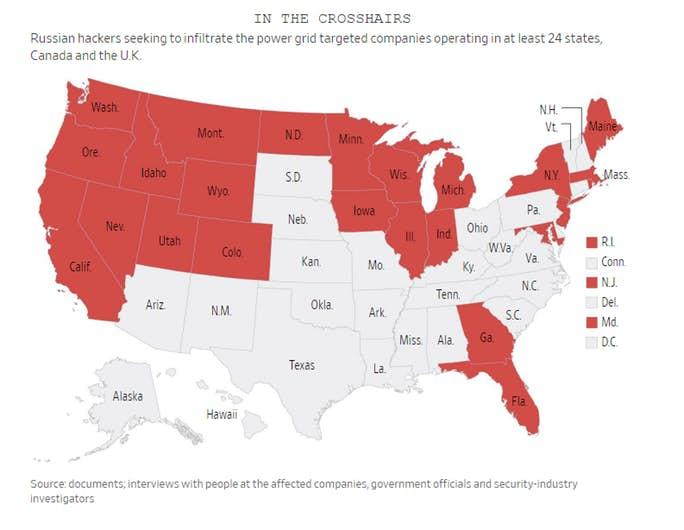
On March 2, 2017, the attackers used Mr. Vitello’s account to send the mass email to customers, which was intended to herd recipients to a website secretly taken over by the hackers.
Once Mr. Vitello realized his email had been hijacked, he tried to warn his contacts not to open any email attachments from him. The hackers blocked the message.
Sneak Attack
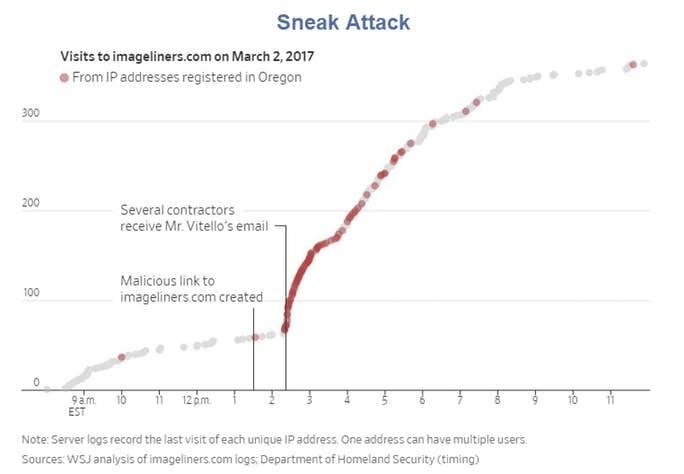
Hackers sent bogus emails from the account of Oregon construction contractor Mike Vitello to herd recipients to a website they had secretly taken over, called imageliners.com. Hackers then used the site to seek access to contractors that do business with U.S. power utilities.
All-Ways Excavating is a government contractor and bids for jobs with agencies including the U.S. Army Corps of Engineers, which operates dozens of federally owned hydroelectric facilities.
One [email] went to Dan Kauffman Excavating Inc., in Lincoln City, Ore., with the subject line: “Please DocuSign Signed Agreement—Funding Project.”
Office manager Corinna Sawyer thought the wording was strange and emailed Mr. Vitello: “Just received this from your email, I assume you have been hacked.”
Back came a response from the intruders who controlled Mr. Vitello’s account: “I did send it.”
Ms. Sawyer, still suspicious, called Mr. Vitello, who told her the email, like the earlier one, was fake.
Federal officials say the attackers looked for ways to bridge the divide between the utilities’ corporate networks, which are connected to the internet, and their critical-control networks, which are walled off from the web for security purposes.
The bridges sometimes come in the form of “jump boxes,” computers that give technicians a way to move between the two systems. If not well defended, these junctions could allow operatives to tunnel under the moat and pop up inside the castle walls.
In briefings to utilities last summer, Jonathan Homer, industrial-control systems cybersecurity chief for Homeland Security, said the Russians had penetrated the control-system area of utilities through poorly protected jump boxes. The attackers had “legitimate access, the same as a technician,” he said in one briefing, and were positioned to take actions that could have temporarily knocked out power.
Attack Still Ongoing
The hack started in 2016 and is still ongoing. The Journal cited many other contractors who were hacked the same way as Vitello. Here's a recent hack.Vello Koiv, president of VAK Construction Engineering Services in Beaverton, Ore., which does subcontracting for the Army Corps, PacifiCorp, Bonneville and Avista Corp. , a utility in Spokane, Wash., says someone at his company took the bait from one of the tainted emails, but his computer technicians caught the problem, so “it was never a full-blown event.” Avista says it doesn’t comment on cyberattacks.
Mr. Koiv says he continued to get tainted emails in 2018. “Whether they’re Russian or not, I don’t know. But someone is still trying to infiltrate our server.”
Last fall, All-Ways Excavating was again hacked.
Battlefield Prepared
Industry experts say Russian government hackers likely remain inside some systems, undetected and awaiting further orders.“What Russia has done is prepare the battlefield without pulling the trigger,” says Robert P. Silvers, former assistant secretary for cyber policy at Homeland Security and now a law partner at Paul Hastings LLP.
Assumptions
Once again, we have assumptions that "Russia is Responsible".The excuse: "The tools and tactics suggested the perpetrators were Russian."
It's a bit of a leap to go from that assumption to the WSJ headline.

No comments:
Post a Comment